3 tips to help make and manage complex passwords by Nick Ismail. Available from <http://www.information-age.com/3-tips-complex-passwords-123462571/> [October 11, 2016] Photo: AdobeStock_21942031-634x0-c-default.jpeg
Passwords, despite the rise of biometrics, are still the most common form of user protection. It is important, therefore, to understand the best methods of producing and managing the most secure passwords possible
Every platform, every service we use requires a password or some other form of authentication.
Remembering dozens, perhaps hundreds, of unique passwords and usernames and keeping all of our devices up to date is difficult, to say the least, and these necessities conflict directly with our desire for maximum convenience.
Most people are guilty of re-using simple passwords across services and of writing them down to make them easier to recall when needed.
In the balancing act between security and convenience, convenience currently has the upper hand at the cost of immeasurable amounts of our most private data.
How can we begin to manage this growing list of passwords in a secure way? Here are 3 key tips and tricks you can use when it comes to password generation and management.
Apply mnemonics
You are probably aware of the rules of password best practice: Passwords must be long; they must contain a mix of characters; they should not be easily guessable; you should never share them; change your passwords often; use different passwords for different applications. The list goes on.
Satisfying all of these criteria can be a challenge, especially when considering that if you create a different password for each service you use you will somehow need to remember each one and avoid writing them down.
An easy way to approach this problem is by applying mnemonics to generating passwords.
For example, take the phrase ‘I would love to fly British Airways first class to Singapore!’ I can easily remember this phrase because it is true and it is not personal.
Also, it doesn’t include a name, an employer, a home location, or any other information about a person that’s easy to guess.
From this phrase, someone can formulate a password by using the first letter(s) of each word, numbers, capitalisation, and special characters.
Suddenly, this sentence creates a strong password that satisfies all the length and complexity requirements set forth by most services: IWLtoFBA1stCtoS!
You can also use other forms of mnemonics, such as misspelling common dictionary words, as a basis for your password instead of just the first letter. Be creative—the important factor is creating a complex password that you can actually remember!
Use a password manager
Though now you know an effective technique for creating passwords, you might still be struggling to remember enough different phrases to cover every account you own.
To help avoid re-using passwords across accounts, you can use password management applications or your web browser’s ability to save and remember passwords.
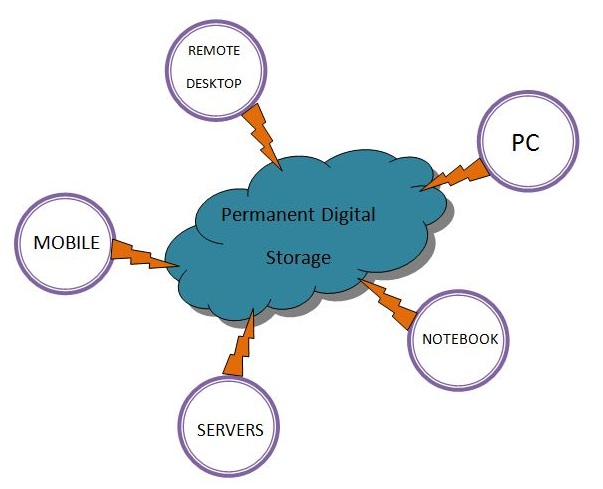
Password managers typically store passwords in the cloud and secure them all with a master password.
If you or your employer are not comfortable with cloud solutions, some password managers offer local storage as an alternative, giving you control and full responsibility over your password store.
However, bear in mind that though password managers are becoming increasingly feature rich, they can be vulnerable just like any other service.
For example, last year password manager LastPass experienced “suspicious activity” and urged users tochange their passwords.
As an alternative, saving passwords in your web browser is also convenient, as some browsers allow you to set a master password as an extra layer of protection, preventing your password from potentially being displayed in clear text.
Add more layers of protection
As well as passwords, you can add other forms of authentication to the data protection mix.
Authentication can be something you know (password), something you have (smart card, token, or mobile device app), or something you are (fingerprint).
On their own, each form of authentication has its weaknesses, but using multiple forms together – known as multi-factor authentication – strengthens the process.
So, even if your passwords are compromised, a malicious actor still needs another authenticator to access your data. Unless they also have access to that second factor, your data remains secure.
Everyone’s responsibility
Effective cybersecurity is not just a matter of installing the right software.
Technical ability alone is not enough to resolve the issue. If it were, breaches wouldn’t occur in such great numbers and with such frequency.
Only a holistic security stance will enable you to limit the opportunities cyber criminals have to steal your organisation’s data.
Preventing breaches requires encouraging secure behaviour at all levels across your organisation.
Every employee, contractor, third party vendor, intern or volunteer should understand the basics of password protection, as well as the basics of identifying, deflecting and reporting potential threats.
That way, if someone succeeds in breaking through your defences, which unfortunately seems inevitable, having a well-educated and aware user base will only help reduce the damage and identify the problem sooner.
Sourced by Stuart Clarke, chief technical officer, cybersecurity, Nuix
3 tips to help make and manage complex passwords by Nick Ismail. Available from <http://www.information-age.com/3-tips-complex-passwords-123462571/> [October 11, 2016] Photo: AdobeStock_21942031-634x0-c-default.jpeg